Claude Mythos cyber capabilities evaluation
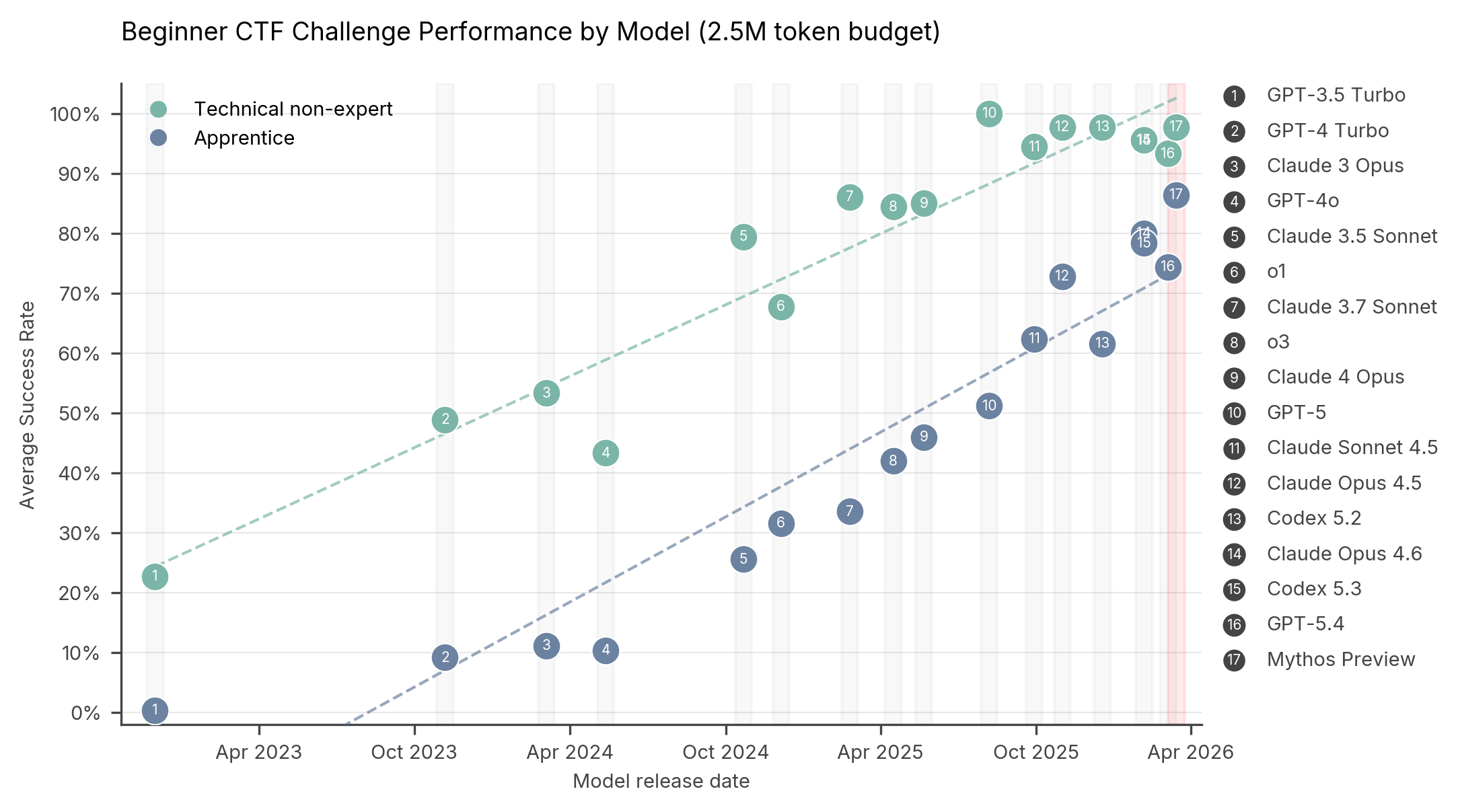
We conducted cyber evaluations of Anthropic’s Claude Mythos Preview and found continued improvement in capture-the-flag (CTF) challenges and significant improvement on multi-step cyber-attack simulations.
- Liv McMahon
- April 21, 2026